

Gauteng-based systems integrators, RAM-TEC Systems, recently purchased a Westermo ED-20 Industrial Router from Throughput Technologies. The purpose of this router is to allow them to establish, via a telephone connection in their Bedfordview offices, a link to a network of Ethernet-based Modicon Quantum PLCs that RAM-TEC have supplied and are currently commissioning at a maize plant in Kenya.
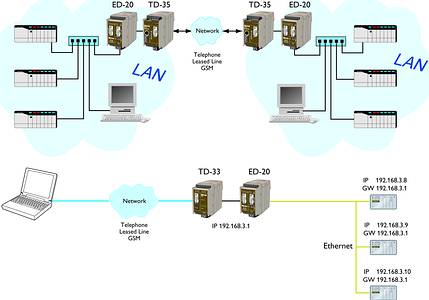
The ED-20 operates in conjunction with other Westermo modems. In this way system integrators and machine manufacturers can connect to remote Ethernet-based control systems anywhere in the world and monitor or re-program Ethernet-based intelligent devices. A software set called ED-Tool is supplied with each unit for the configuration task.
Another feature of the ED-20 is that it can be used to connect remote Ethernet local area networks (LAN) in different locations. An example of this in the UK is an application for a major train tunnelling system currently in progress under London. Along the tunnel there are 14 ventilation systems each with a PLC and its associated equipment, all of which are connected to a LAN at the specific site.
Utilising Westermo GSM (cellular) modems, the operator at a central control room is able to start and stop ventilation fans, dependent on requirements (central LAN to remote LAN). In addition any fault at any one of the 14 locations is relayed back to the central location from the PLC to the central control room (remote LAN to central LAN). The ED-20 is able to initialise the GSM Modem, to establish the link.
PPP (the point-to-point protocol) is a mechanism for creating and running TCP/IP over a serial link - a direct serial connection or a link made using one of the following: Westermo analog public service telephone network (PSTN), leased line (dedicated telephone or fixed lines), GSM (cellular), fibre or short-haul modems. Other computers can connect via the ED-20 and communicate over the PPP link using File Transfer Protocol (FTP), Telnet, Web, etc. in the same manner as with an Ethernet TCP/IP link. One major difference between a PPP and an Ethernet connection is of course the speed. A standard Ethernet connection operates at 10 Mbit/100 Mbit maximum theoretical throughput, whereas an analog modem operates at speeds up to 56 kbit.
PPP is strictly a peer-to-peer protocol; there is no difference between the machine that dials in and the machine that is dialled into. However, it is still useful to think in terms of servers and clients. When you dial into a site to establish a PPP connection, you are considered the client. The machine to which you connect is considered the server.
ED-20 has two network interfaces, Ethernet and PPP, so the unit can forward IP-packets between these interfaces. Ethernet interface is a part of the local network and the 'Local IP Address' and 'Subnet Mask' must be set to the right 'Network ID'. The PPP connection can be established over PSTN, leased line or private lines. ED-20 can act as a PPP Server, PPP Client or both (see information on the tunnelling application mentioned above). These functions are set on the 'Modem settings' tab in ED-Tool for ED-20.
Brouter function
The Brouter function will establish a dial-up connection when valid outbound IP address (defined on the tab 'Brouter Settings' in ED-Tool for ED-20) is sent to the ED-20.
Proxy ARP function
The Proxy ARP function can be activated and used to divide an existing network into several networks and keep the original IP address settings, ie, the networks would appear to be one single network instead of multiple networks connected to each other. This will allow the connected equipment to communicate to each other without using gateways and is a benefit when attaching equipment not supporting gateway functionality.
More and more industrial applications are making use of Ethernet as their preferred data networking method. The ED-20 provides a simple and cost effective means of connection to remote LANs, thereby enhancing the overall possibilities of control and monitoring over long distances.
| Tel: | +27 11 705 2497 |
| Email: | [email protected] |
| www: | www.throughput.co.za |
| Articles: | More information and articles about Throughput Technologies |

© Technews Publishing (Pty) Ltd | All Rights Reserved