Top five e-threats – April 2010
May 2010
IT in Manufacturing
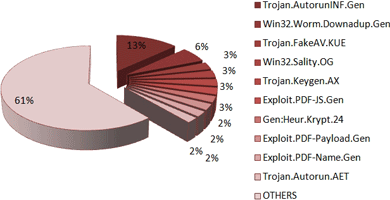
April’s top brings forward two newcomers: a fake AV and a Trojan.Keygen!
April is the third month in a row in which Trojan.AutorunInf.Gen is the top e-threat with 13,21% of the total amount of the global malware. This reveals that removable devices are used on a large scale and their owners are not that aware – still – of the damage waiting for them in the tiny gadgets.
Win32.Worm.Downadup.Gen (Kido or Conficker) is to be found once again shadowing the top Trojan.AutorunInf.Gen with 5,77%. It is the result of a successful exploitation of a Microsoft Windows vulnerability and unfortunately people are hesitant towards updating their operating systems and antivirus solution so as to easily get rid of this obstinate worm.
Ranking third is a newcomer - Trojan.FakeAV.KUE - with a percentage of 2,72 of the total amount of infections. It is not much of a surprise here, since this past week has been mostly about rogue AV. This detection covers JavaScript code that is used to trigger fake alerts on websites connected to the placement of rogue antivirus software. These scripts are hosted on malicious sites and innocent
victim-pages that have been infected.
Win32.Sality.OG is positioned fourth (2,72%) in April’s malware chart, exactly as last month - again as the sole representative of the file infector software. Shielded by a polymorphic packer, the Sality family is extremely difficult to detect and annihilate. In addition to that, the rootkit component of the virus tries to disable various antivirus applications installed on the infected system.
The second new comer of this month’s is Trojan.Keygen.AX – April’s top number five, which intercepts and blocks threats related to cracks, patches and keygens. Generating keys and patches for various applications is a common practice for commercial software on the Internet, P2P platforms, and instant messenger, download sites, social networking environments. It may be popular, but it is also illegal and risky. So, play fair and safe!
Overview of April’s malware distribution chart:
BitDefender’s April 2009 top 10 e-threat list includes:
1. Trojan.AutorunINF.Gen 13,21
2. Win32.Worm.Downadup.Gen 5,77
3. Trojan.FakeAV.KUE 2,72
4. Win32.Sality.OG 2,72
5. Trojan.Keygen.AX 2,66
6. Exploit.PDF-JS.Gen 2,57
7. Gen:Heur.Krypt.24 2,38
8. Exploit.PDF-Payload.Gen 2,34
9. Exploit.PDF-Name.Gen 2,12
10. Trojan.Autorun.AET 2,05
Others 61,40
For more information contact Alina Anton, senior PR and marketing coordinator, EMEA & APAC business unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com
Further reading:
Siemens ecosystem strengthens data and AI integration
Siemens South Africa
IT in Manufacturing
Siemens has announced significant expansions to its Industrial Edge ecosystem, accelerating data and AI integration and releasing enhanced cybersecurity functionalities. These enable a seamless integration of IT and OT environments, optimise processes and reduce operational disruptions.
Read more...
Siemens manages shipbuilding process for HD Hyundai
Siemens South Africa
IT in Manufacturing
Siemens has been selected by HD Korea Shipbuilding & Offshore Engineering as a preferred partner to establish an integrated platform to manage the entire shipbuilding process as a single data flow to help ensure consistency across all its global shipyard facilities.
Read more...
Transforming the process industry through digitalisation
Endress+Hauser South Africa
IT in Manufacturing
By connecting field devices, systems and people, digitalisation creates new opportunities to optimise operations, enhance maintenance strategies and support continuous improvement. As a leading instrumentation provider and major source of process data, Endress+Hauser plays a key role in enabling this transformation.
Read more...
The OT operator’s guide to security and uptime on the plant
RJ Connect
IT in Manufacturing
The article addresses three common questions about industrial network deployment and maintenance, exploring ways to achieve better control and visibility with more efficiency.
Read more...
The assets you can’t see are the ones that can shut you down
IT in Manufacturing
ABEGuardOT is an asset management solution that delivers continuous, non-intrusive visibility across multi-vendor environments, including Siemens, Rockwell, ABB, Honeywell, Schneider Electric, Emerson, GE and Yokogawa, with support for OPC UA, EtherNet/IP, Modbus and Profibus.
Read more...
Edge I/O NTS and the need for industrial speed
Schneider Electric South Africa
IT in Manufacturing
One of the most compelling solutions to emerge from industrial automation is Edge I/O NTS, which represents a natural evolution of computing from centralised servers to localised, device-level input/output processing, offering improved speed, efficiency and resilience.
Read more...
The next wave of AI-driven process automation
Schneider Electric South Africa
IT in Manufacturing
As process industries hurtle toward an AI-driven future, four powerful trends are set to redefine automation strategies in 2026: hyper automation, AI-first automation, low code/no code platforms, and advanced process intelligence.
Read more...
Huge increase in denial-of-service cyber threats
IT in Manufacturing
NETSCOUT has released its Distributed Denial-of-Service Threat Intelligence report, revealing sophisticated attacker collaboration, resilient botnets and compromised IoT infrastructure that drove more than eight million DDoS attacks worldwide.
Read more...
Sustainable manufacturing
ABB South Africa
IT in Manufacturing
ABB’s production facility in Shandong province, China is delivering measurable energy and emissions reductions through the implementation of advanced digital energy management and electrification solutions.
Read more...
Open automation is breaking legacy chains
Schneider Electric South Africa
IT in Manufacturing
Industrial automation is now entering a new era defined by open, software-driven principles that are breaking decades of hardware-bound limitations.
Read more...