

In February 2021, an unidentified intruder gained access to the network systems of a US water treatment plant in Oldsmar, Florida and briefly altered the chemical levels in the drinking water. Fortunately, an employee noticed the intrusion attempt and blocked it immediately. This incident sparked many discussions on the topic of cybersecurity in operational technology (OT) environments.
Digital transformation and today’s industrial networks
By adapting through digital transformation, OT network infrastructure starts growing in scale and becomes increasingly complex and interconnected. A single point of failure could bring tremendous harm to the whole networking system. Therefore, ensuring maximum network uptime is critical to keep business running smoothly.
Remote network management is becoming an invaluable tool for handling emergencies quickly and efficiently. However, there are multiple obstacles hampering the use of remote services, with cybersecurity being the biggest concern. Nowadays, cyberattacks are a common occurrence. Without cybersecurity, the door is left wide open for malicious individuals to take advantage of vulnerable networks. Looking back at the Florida water treatment facility case, the FBI assessed that the intruder likely accessed the facility’s systems by exploiting cybersecurity weaknesses, including poor password security and the lack of firewall protection when logging in to the plant’s systems remotely, as well as using unsafe remote access software.
Pay special attention to OT requirements
Considering the requirements of secure remote network management, everyone is looking for a solution that could help simplify daily operations without having to worry about cybersecurity. While there are many pieces of software available designed for remote access or network management, they often cater to IT networks and are rarely part of larger, consolidated solutions. However, OT and IT networks have different characteristics and priorities. While IT prioritises data confidentiality, OT focuses on network availability and zero tolerance for downtime. This difference in approach makes it difficult for OT networks to adopt IT practices. Another hurdle is that many automation engineers are not familiar with VPNs, or know the public IP necessary for setting up remote access.
Convenient and secure remote maintenance in practice
For OT engineers, cybersecurity remains the number one concern. A solution with flexible access control could fulfil different OT scenarios and enhance network security. For example, customisable access control lets facility owners decide when and for how long third-party engineers can access their network. Furthermore, access can be restricted to specific network areas. These measures can ensure the safety of their network when opening the door for remote maintenance services. Remote services for OT should also be accessible and easy to use. An ideal solution lets OT engineers easily set up remote access when needed, even if they are not familiar with VPNs or know the public IP.
With purpose-built and consolidated solutions, different players in the OT world would be able to enjoy the benefits of remote network management. Let’s take a look at how this works in two different customer scenarios:
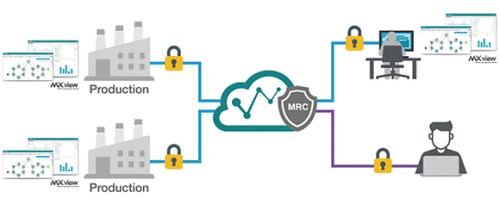
1. Facility owners
Manufacturers with facilities scattered across multiple locations require expansive networks to sustain operational effectiveness and efficiency. To manage such large and disperse networks, the network management software installed at the remote sites monitors the local network and sends data back to the HQ control centre through an encrypted tunnel. This gives engineers a complete view of the network from a central location for remotely managing operations at each site. If any incident occurs, engineers at the headquarters can remotely access the on-site network device via a secure VPN connection or call in the help of third-party support services if necessary, using an on-demand encrypted VPN tunnel (Figure 1).
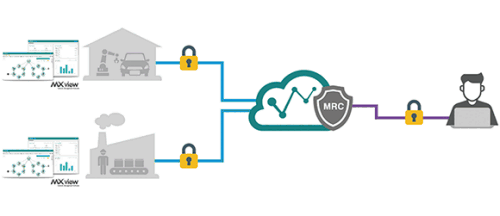
2. Service providers/system integrators
To help their customers manage and maintain their networks, network service providers require a simple solution for responding to requests from multiple customers, solving issues as quickly as possible. Real-time remote service allows service providers to overcome geographical limitations and streamline their customer service. An on-demand encrypted VPN tunnel can let support engineers easily access the network management software at the customer’s site without jeopardising the safety of the customer’s network (Figure 2).
| Tel: | +27 11 781 0777 |
| Email: | [email protected] |
| www: | www.rjconnect.co.za |
| Articles: | More information and articles about RJ Connect |

© Technews Publishing (Pty) Ltd | All Rights Reserved