Office 2010 beta impersonator is Trojan
May 2010
IT in Manufacturing
The 'big name' cybercrime series continues with an alleged Office 2010 Beta version used as bait.
Just a week after the alert on the fake Windows 7 compatibility checker, another interesting e-mail came into Inbox. The subject? 'See Office 2010 Beta in action'.
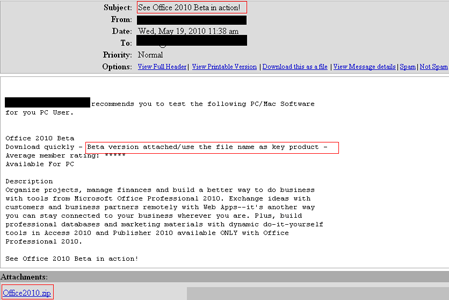
Figure 1. The sham Office 2010 Beta announcement
This enticing title accompanies a message which reveals to the user what is new in this Office version. Rated by members with five stars (out of five, of course), this Beta version appears too hot not to be tested. It is like … a must. To save the users’ time and get them down to this ardent matter as soon as possible, the promised beta version is attached to the message as a zip file. Quite suspicious, is it not?
When extracting it, the attachment reveals me an exe file baptised under a baffling string of letters and figures, much in the style of a product key. This name is actually the product key users must input in order to activate the beta product.
However, a detailed file check exposes the fake beta as malware.
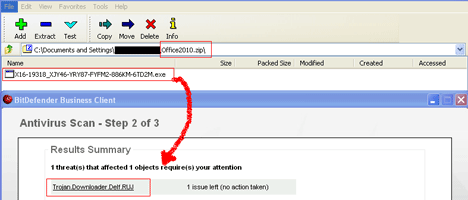
Figure 2. The Beta impersonating Trojan
Identified by BitDefender as Trojan.Downloader.Delf.RUJ, this piece of malware affects the Windows platform. It is designed to infiltrate the user’s computer and open a conduit by which large amounts of adware and spyware can be piped into the affected system, therefore generating loads of popup adverts. Once installed, the Trojan creates a copy of itself into the and the registry is modified to run the respective copy at each Windows startup. Then, it attempts to connect to a specific IP address to download different malicious files. Trojan.Downloader.Delf.RUJ is also a very dangerous threat to personal and financial data.
In order to stay safe, never open attachments without scanning them first. Install and update a complete antimalware software solution and, if you want to test software, make sure you download it from the official vendor’s website.
All product and company names mentioned herein are for identification purposes only and are the property of, and may be trademarks of, their respective owners.
For more information contact Alina Anton, senior PR & Marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com
Further reading:
Siemens ecosystem strengthens data and AI integration
Siemens South Africa
IT in Manufacturing
Siemens has announced significant expansions to its Industrial Edge ecosystem, accelerating data and AI integration and releasing enhanced cybersecurity functionalities. These enable a seamless integration of IT and OT environments, optimise processes and reduce operational disruptions.
Read more...
Siemens manages shipbuilding process for HD Hyundai
Siemens South Africa
IT in Manufacturing
Siemens has been selected by HD Korea Shipbuilding & Offshore Engineering as a preferred partner to establish an integrated platform to manage the entire shipbuilding process as a single data flow to help ensure consistency across all its global shipyard facilities.
Read more...
Transforming the process industry through digitalisation
Endress+Hauser South Africa
IT in Manufacturing
By connecting field devices, systems and people, digitalisation creates new opportunities to optimise operations, enhance maintenance strategies and support continuous improvement. As a leading instrumentation provider and major source of process data, Endress+Hauser plays a key role in enabling this transformation.
Read more...
The OT operator’s guide to security and uptime on the plant
RJ Connect
IT in Manufacturing
The article addresses three common questions about industrial network deployment and maintenance, exploring ways to achieve better control and visibility with more efficiency.
Read more...
The assets you can’t see are the ones that can shut you down
IT in Manufacturing
ABEGuardOT is an asset management solution that delivers continuous, non-intrusive visibility across multi-vendor environments, including Siemens, Rockwell, ABB, Honeywell, Schneider Electric, Emerson, GE and Yokogawa, with support for OPC UA, EtherNet/IP, Modbus and Profibus.
Read more...
Edge I/O NTS and the need for industrial speed
Schneider Electric South Africa
IT in Manufacturing
One of the most compelling solutions to emerge from industrial automation is Edge I/O NTS, which represents a natural evolution of computing from centralised servers to localised, device-level input/output processing, offering improved speed, efficiency and resilience.
Read more...
The next wave of AI-driven process automation
Schneider Electric South Africa
IT in Manufacturing
As process industries hurtle toward an AI-driven future, four powerful trends are set to redefine automation strategies in 2026: hyper automation, AI-first automation, low code/no code platforms, and advanced process intelligence.
Read more...
Huge increase in denial-of-service cyber threats
IT in Manufacturing
NETSCOUT has released its Distributed Denial-of-Service Threat Intelligence report, revealing sophisticated attacker collaboration, resilient botnets and compromised IoT infrastructure that drove more than eight million DDoS attacks worldwide.
Read more...
Sustainable manufacturing
ABB South Africa
IT in Manufacturing
ABB’s production facility in Shandong province, China is delivering measurable energy and emissions reductions through the implementation of advanced digital energy management and electrification solutions.
Read more...
Open automation is breaking legacy chains
Schneider Electric South Africa
IT in Manufacturing
Industrial automation is now entering a new era defined by open, software-driven principles that are breaking decades of hardware-bound limitations.
Read more...