
Husbands and teenage children need to pay great attention to on-line transactions of all kinds
According to an independent research conducted by Dept Information System, University of Cape Town “the national economy [of South Africa] will become increasingly reliant on IT infrastructure and e-commerce for critical activities. Future growth may be hindered by the constantly evolving threat of computer crime, and thus it imperative that South African organisations are made aware of and become more knowledgeable of the origins and consequences of computer security issues, in the hope that further investment will be made into computer and information security for improvement”. This is exactly the reason why people need to understand the threats Internet poses and work with AV specialists to find ways to protect themselves and their families against cybercrime.
Unfortunately, only few of the Internet users are actually aware of the threats lurking in the Internet jungle. Here are a few examples of such dangers:
1. The web being the very next best thing when it comes to shopping for gifts, most computer users will point their browser to their favourite online store with the credit card details at hand. Credit card credentials can get into the hands of ill-meaning third parties either as the result of a successful phishing attempt or of a Trojan with keylogging capabilities having compromised the system prior to the purchase.
2. Spammers will most definitely take a chance at piggybacking on the event so as to advertise bargains that would make excellent gifts for women. These knockoffs might be pieces of jewellery, accessories, as well as sexual enhancement pills or other prescription-based drugs. Social networks are other vulnerable spots that cybercriminals choose to exploit. They might become channels for spam and phishing messages made to trick the user into willingly sharing his/her credentials most of the times without assuring ahead of the credibility of the source of the message.
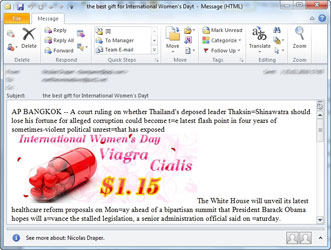
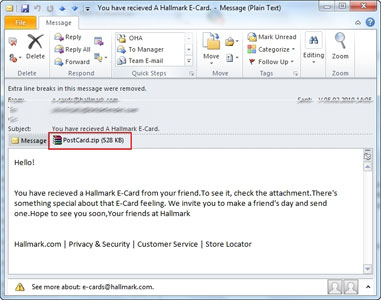
3. Malware-bundled greeting cards are also expected to proliferate. They usually carry various hidden e-threats, especially variants of zBot as well as the infamous Koobface worm. All sorts of malware can reach the user 'nicely' wrapped in a spam message:
4. Identity theft should be yet another major concern for online shoppers while filling-in personal information in order to buy the gift of their dreams. The rules that apply here are never to visit and use an online store that promotes its services through spam mail and not to provide more personal information than it is necessary for shipping and billing.
Here are some e-safety guidelines for your online quest during Mother’s Day:
* Using a complete anti-malware solution, such as BitDefender Total Security, will solve most of these problems, as it can block spam, phishing attempts and prevent malware from infecting your computer, therefore keeping your private data safe.
* Exercise caution when you add personal data to your accounts. Keep the critical data to a safe minimum. Do not disclose important information such as social security number, date of birth, home address or phone number, before you know for sure who you are talking to.
* Pay great attention to the links you visit and do not download any content before you are absolutely sure that it comes from a trustworthy person.
* Do not check your e-banking account from public computers connected to Internet (like those in a library or Internet Café).
* If you use a wireless connection, make sure that your connection is secured and encrypted and that you know and trust the owner of the access point; also, refrain from using an unsecured public wireless connection (like those in airports or hotels) when banking over the Internet. Still, if forced to do so, use an on-screen (virtual keyboard) to enter sensitive data. Although not 100% bulletproof, this technique would guard your data from average keylogger applications.
* Make sure that the e-banking Web site uses SSL encryption (Secure Socket Layer) and security authentication methods - look for the 'https' prefix and the locked padlock. If you are requested to accept a certificate for the session, check that the name on the certificate matches the name of the institution you wish to deal with and that the certificate is signed by a known Certificate Authority such as Thawte or VeriSign before accepting.
* Avoid using a non-secured computer (like a friend's desktop or job colleague laptop). Still, if you are forced to do so, make sure you at least run BitDefender's advanced scanning on-line tool, Quick Scan, before proceeding.
For more information contact Alina Anton, senior PR & marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com

© Technews Publishing (Pty) Ltd | All Rights Reserved