
Industrial cyber security targeting brownfields
How much technology is needed in brownfield applications to reach an acceptable security risk level?
To discuss this and related questions, ARC invited industrial security experts from HIMA, Innominate AG, and ISA to the workshop to review the current situation with workshop participants. The first recommendation was: ‘Determine your security priority areas’.
Important areas to achieve cyber security
The experts advised end users to focus on four areas:
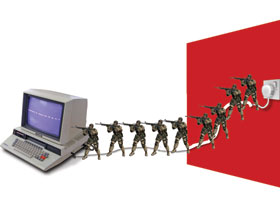
1. Separate the automation network from the office network (untrusted, because of its connectivity to Internet).
2. Ensure secure remote support capabilities from inside and outside the company.
3. Keep an eye on supplier access to control systems wherever possible – this may be the biggest challenge.
4. Protect the automation systems from malware attacks through PCs by removing PCs from the manufacturing network by connecting them to the office network (if possible), and isolating PCs at the edge of the network and implementing a firewall to connect them securely to the manufacturing network.
Big security models not required
After establishing security areas, the user needs to implement solutions. Many users won’t need big security models involving complex acronyms and sophisticated security appliances. Vendors need to stop presenting security this way and users should stop being paralysed by the thought of its complexity. After assessing the actual needs of the user, vendors need to focus on those needs.
The first steps to a better security concept might be to define and implement a strategy for Ethernet-based automation systems. If the user needs help, he can simply refer to security standards, contact the automation vendor, or engage a consultant for tailor-made support.
Many control engineers don’t have experience with industrial security and Ethernet-based control networks. External training may be required to understand the basic security principles and motivate control engineers to get acquainted with them.
The fact that a plant has not experienced a security breach in the past is not a reason to feel secure. The threat level rises continuously and it is only a matter of time until something bad occurs in an unprotected system.
Many incidents originate from inside the plant. Maintenance people are not always aware that they can cause damage if they connect a PC via USB or Ethernet to the automation network. Those threats are often unintentional.
Think about network traffic control and fast recovery after security breaches. It is nearly impossible to prevent every attack, but there should be a strategy in place to recover from them.
Non-intrusive industrial security
Due to its operational requirements, process automation demands a different set of safeguarding measures than classical office IT. Particularly challenging for users is patch management (regular update of operating systems, application software, and virus protection) and intrusion detection (recognising unknown intruders or malware in automation networks). Operators carry the responsibility for their installations. Suppliers are called upon to develop automation security solutions that ensure maximal plant availability and security for both greenfield and brownfield installations.
The approach
Sensibly configured, decentralised firewalls are the most effective, quantifiable means to reduce the risk of network-based disruptions to machines and installations. At the TCP/IP communication level, firewalls can reduce this risk by several orders of magnitude. A closer look at the communication on lower Ethernet levels even shows a growth of the ratio between possible and needed connections by a factor of five to six. Keeping billions of useless data packets away from installed automation technology would not just prevent denial-of-service (DOS) attacks, but also unauthorised and fraudulent access attempts.
Industrial norms for industrial security management like ISA99 or IEC 62443 suggest firewall segmentation between the automation level and the definable measurement and control areas as best practice. Furthermore they recommend the creation of a stringent isolation zone (DMZ) between the enterprise and the process network to prevent direct communication.
Firewalls, used as routers, are suited for segmenting, masking or network address translation (NAT) in newly constructed plant networks in which appro-priate routing structures can be planned from the outset. Retrofitting them into existing plants is difficult or even impossible as the necessary constructions and conversions would be too expensive for the mostly flat network structures.
Industrial security appliances are well-suited for network security retrofits of existing plants, as the devices not only serve as routers but can also operate in a transparent ‘stealth mode’.
Even with firewalls, a residual risk remains for the remaining legitimate connections to be used by attackers or malware. The Windows client and server components, which are frequently under the threat of direct attacks, should be protected through an integrity monitoring procedure, as it recognises manipulations and violations of the system integrity in reliable and non-invasive way.
For more information contact Paul Miller, ARC Advisory Group, +1 781 471 1126, [email protected], www.arcweb.com
© Technews Publishing (Pty) Ltd | All Rights Reserved